How to Build HIPAA-Compliant Software Without Overengineering It
How to build HIPAA-compliant healthcare software without overengineering it — modular, secure, and built for real-world scale.
How to Build HIPAA-Compliant Software Without Overengineering It
Healthcare software has a reputation for being slow, expensive, and overcomplicated—and for good reason. With regulations like HIPAA, sensitive patient data, and legacy systems in play, many teams default to overbuilding everything “just in case,” which leads to bloated systems, slow delivery, and high costs.
In reality, you don’t need to overengineer to be compliant—you just need to engineer correctly.
Why This Is Hard
Healthtech sits at the intersection of:
- privacy
- compliance
- real-time operations
- human-critical outcomes
Regulations like HIPAA require strict control over:
- Protected Health Information (PHI)
- access and permissions
- data storage and transmission
- audit trails
At the same time, modern products demand:
- speed
- usability
- integrations (EHRs, APIs, devices)
- AI capabilities
This creates a common trap:
👉 teams confuse compliance with complexity
The Wrong Way
1. Overbuilding security layers
Adding redundant systems, excessive controls, and unnecessary abstractions.
Result: slow performance, high costs.
2. Treating compliance as documentation
Writing policies without aligning actual system behavior.
Result: audit risks.
3. Ignoring architecture early
Building first, securing later.
Result: expensive rewrites.
4. Locking everything down
Over-restricting access, slowing down users and internal teams.
Result: poor adoption.
The Right Way: Compliance by Design
Modern healthcare platforms follow a simpler principle:
Build only what is required — but build it correctly.
This aligns with guidance from the U.S. Department of Health and Human Services, which emphasizes risk-based implementation of safeguards, not unnecessary complexity.
Step 1 — Understand What HIPAA Actually Requires
HIPAA is not prescriptive about tools.
It defines outcomes, not exact implementations.
Core requirements:
- ensure confidentiality, integrity, and availability of PHI
- protect against threats and unauthorized access
- provide auditability and accountability
According to U.S. Department of Health and Human Services, safeguards fall into three categories:
- administrative
- physical
- technical
👉 Your job is not to overbuild.
It’s to cover these areas effectively.
Step 2 — Build Modular Security Layers
Instead of one complex system, break security into modules:
- authentication & authorization
- data encryption
- audit logging
- data storage & access control
Each module should be:
- isolated
- testable
- replaceable
This approach aligns with modern healthtech architecture, where modularity improves both compliance and maintainability.
👉 Think in systems, not features. See our HIPAA compliant case for reference.
Step 3 — Use Proven Infrastructure
You don’t need to reinvent security.
Cloud providers like Amazon Web Services, Google Cloud, and Microsoft Azure offer:
- HIPAA-eligible services
- encryption tools
- identity management
- audit logging
These platforms are widely used in healthcare because they already implement many required controls.
👉 Build on top of secure infrastructure — don’t rebuild it.
If you are a healthtech startup, don’t repeat the mistakes of others trying to reinvent the wheel.
Step 4 — Design for Least Privilege
One of the most effective (and simple) principles:
Give users only the access they need — nothing more.
This includes:
- role-based access control (RBAC)
- segmented data access
- session management
According to healthcare security best practices, access control is one of the most critical safeguards for PHI protection.
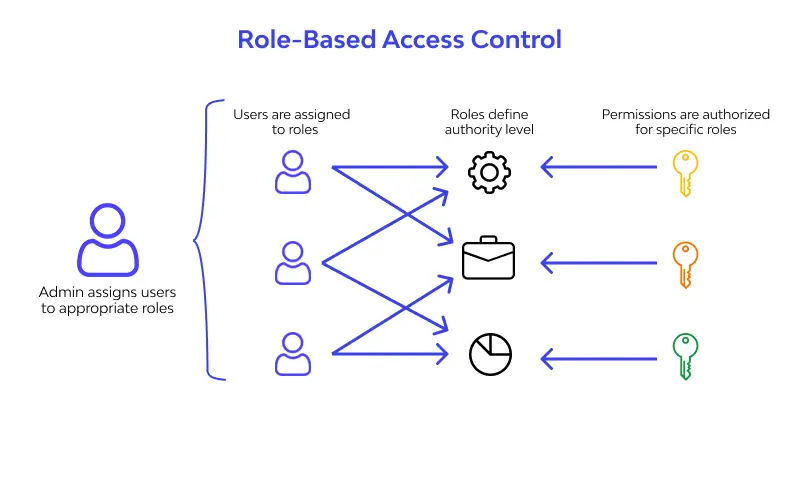
👉 This reduces risk without adding complexity.
Step 5 — Make Auditability a Core Feature
Compliance depends on visibility.
Your system must answer:
- who accessed what data
- when
- what actions were performed
This requires:
- structured logs
- immutable records
- monitoring tools
Auditability is not optional — it’s essential for both compliance and debugging.
Step 6 — Integrate, Don’t Isolate
Healthcare systems rarely operate alone.
They connect to:
- EHR systems
- insurance providers
- medical devices
- third-party APIs
The challenge is maintaining compliance across integrations.
Best practice:
- use secure APIs
- encrypt data in transit
- validate external inputs
👉 Integration is part of your security model.
Step 7 — Align Compliance with Product Design
According to research from Deloitte, successful healthtech platforms embed compliance into product workflows, not just infrastructure.
That means:
- secure onboarding flows
- clear consent mechanisms
- transparent data usage
👉 Compliance should improve user trust — not block usability.
Real-World Pattern
Modern digital health platforms — from telemedicine apps to patient portals — follow similar principles:
- modular architecture
- cloud-native security
- built-in auditability
- integration-ready systems
They don’t overbuild.
They build intentionally.
Builder Takeaways
If you’re building healthcare software:
- focus on requirements, not assumptions
- use modular security architecture
- leverage proven cloud infrastructure
- implement least-privilege access
- design auditability from the start
- treat integrations as part of compliance
Most importantly:
Compliance is not about doing more.
It’s about doing the right things well.
Final Thought
HIPAA compliance doesn’t require overengineering.
It requires clarity.
At Unibrix, we approach healthcare software the same way we build everything:
Structured systems.
Secure foundations.
Flexible, modular architecture.
Serious software — built with the joy of play.
If you're building healthcare software and want to stay compliant without overengineering — we can help you design it right.

Moombix

Kennitalan

Wooskill
technical assessment,
and project scoping.
UI/UX design, and
technical specifications.
reviews, and continuous
integration.
testing, security audits,
and bug fixes.
documentation, and
ongoing support.